Blockchain technology has revolutionised an array of fields including financial services, supply chain, healthcare and the Internet of Things. In the first of a series of blogs exploring blockchain, we look at the key areas to consider before deciding to invest in blockchain – an overview of the technology, its business applications and strategic business values.
What is a blockchain?
A blockchain is a shared, decentralised database that uses Distributed Ledger Technology (DLT) to store data in a succession of segments called blocks. After the latest block is filled, it is cryptographically connected to the previous completed block. The data chain created is called a blockchain.
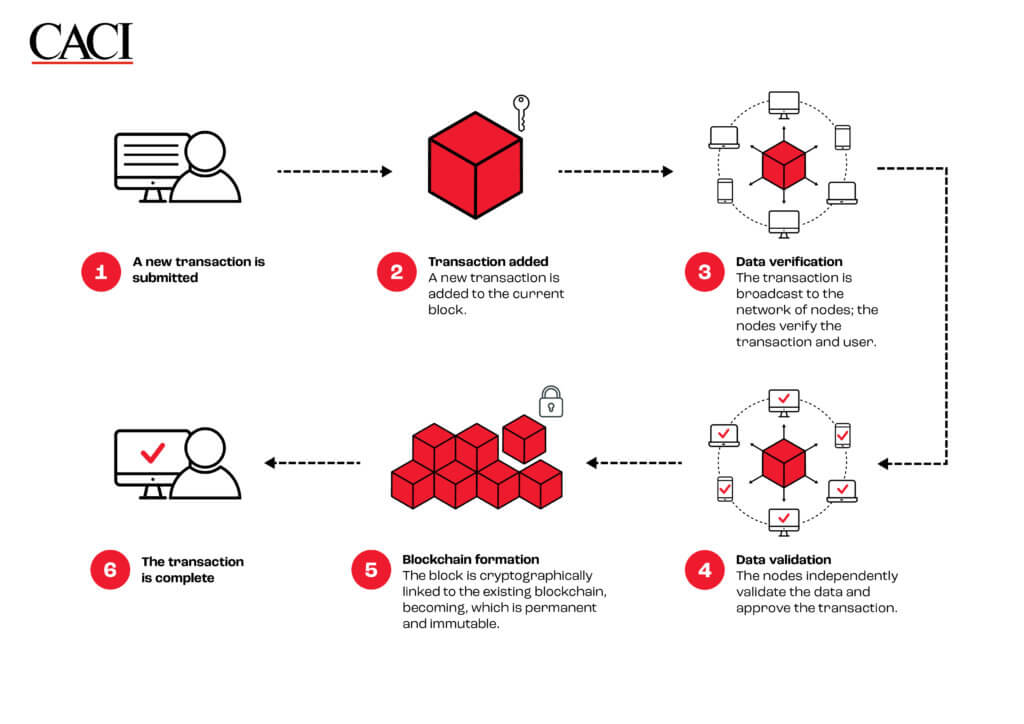
How does it work?
What types of blockchain are there?
Public blockchain
A public blockchain is non-restrictive and permissionless. Any internet user can register on a public blockchain platform and become an authorised processing and storage node. All nodes in the network have equal rights to access, create, and validate the data in the blockchain. Bitcoin and Ethereum are the most well-known public blockchain platforms dealing with cryptocurrency.
Private blockchain
A private blockchain works in a restrictive environment and is governed by one organisation which determines node access, executes the consensus protocol and maintains the shared data. A private blockchain typically runs within an organisation’s network to cope with highly confidential data and is held securely. Audit management and asset control are common use cases of private blockchain.
Hybrid blockchain
A hybrid blockchain combines characteristics of both public and private blockchains to control access to specific private data held on a public blockchain. For instance, property companies use hybrid blockchains to run systems privately but disclose certain transaction information to the public.
Consortium blockchain
Consortium blockchains are a type of private blockchain managed by multiple organisations rather than one entity. Supply chain management, especially for food and medicine, is an ideal application for this type of blockchain – from sourcing to delivery, all parties involved in the supply chain can form a consortium to track the product status.
The advantages of blockchain
Decentralised trust
Users no longer rely on centralised intermediaries to complete transactions. By storing data in a peer-to-peer network, every node has the same data and authority to view all transactions. There is no single point of control.
Enhanced security
Cryptographic hashing, which converts arbitrarily large amounts of data into a short unique string of text, plays a crucial role in blockchain security. A hash value is automatically calculated for each block and consists of the block’s ID number, user ID number, previous block’s hash value, timestamp and other details. Employing hashing in this manner makes it impossible to change any data held in the block, metadata about the block, or its position in the chain without having to recompute that and every subsequent block in the chain.
High level of data integrity
From the verification process to storing transactions, data is verified by a consensus algorithm specific to the blockchain protocol. Any invalid data is rejected, protecting the chain from human error. The integrity and security of blockchains make them immutable, transparent and unimpeachable.
Disadvantages of blockchain
Uncertain legal and regulatory environment
Blockchain technology is still developing and the principles of existing regulations may not accommodate the fundamentals of blockchain. For instance, General Data Protection Regulation (GDPR) assumes data is centralised on at least one legal entity, while blockchain decentralises data storage to an anonymous network of nodes. Blockchain technologists should study the regulations thoroughly before implementation.
Novel cyber-attacks
Blockchains are not immune to cyber-attacks and all new technologies have undiscovered vulnerabilities. Attacks such as the following are effective against blockchain:
- a 51% attack – where more than half of the nodes computing a chain are influenced by a bad actor
- a Sybil attack – where a single entity creates multiple dummy nodes to wield disproportionate voting power
- DDOS – where nodes are flooded with connections which block out legitimate traffic
There are no quick solutions to safeguard your systems, blockchain technologists can implement careful plans on system architecture and design to pre-empt cyber-attacks.
High energy consumption and data storage cost
Older blockchains, such as Bitcoin, validate blocks using a Proof of Work consensus algorithm in which all the nodes compete to compute a completed block in exchange for an administrative payment. Only one node can win resulting in all the partial computations being wasted. This amounts to a tremendous waste of electricity. More modern blockchains employ Proof of Stake, which is much more efficient, but migrating from one protocol to the other is extremely complicated. Blockchains ledgers – the data chain – are replicated at least in part to every node. By 2021, the Bitcoin ledger had reached 433GB [1] and the Ethereum ledger close to 1TB [2]. Given node counts in the thousands, even partial replication represents vast duplication across the world.
Considerations before you implement blockchain
Business needs
Before you implement blockchain technology, we strongly advise your team to evaluate existing business models and needs. Businesses that require a high level of data integrity and traceability are more likely to apply this. Investing in blockchain technology is worthwhile if the application transforms your user experience, democratises governance or reduces overall cost; but it is fundamentally a distributed database.
Integration concerns
Given that most organisations rely on legacy systems to run their business, careful technical analysis is essential to ensure that blockchain systems can integrate successfully with the existing estate.
Privacy issues
Logical layers in a blockchain system are the key to complying with privacy regulations. Stakeholders should examine the interactions between different layers – how the data is stored, accessed and transacted in the system.
Cost and revenue analysis
Enormous investments in setting up a blockchain system – such as infrastructure, data storage and maintenance – often create barriers for organisations to get involved. However evaluating its strategic business values can change your mind. Let’s take some examples from The Blockchain 50, named by Forbes [3] :
- Allianz streamlines cross-border auto insurance claims in Europe. Processing time for insurance claims has been reduced from several months to minutes and costs have fallen 10%. The quick claim procedure absolutely contributes to a high customer satisfaction level and customer retention. No wonder Allianz has led in the claims category with a satisfaction score of 76.04%, according to Brokerbility’s survey. [4]
- Boeing builds a digital aircraft record system to help airlines keep up with required maintenance, saving 25% on maintenance costs, potentially worth up to $3.5 billion (~£2.96 billion) annually.[5]
- De Beers has registered over 400,000 gems worth $2 billion (~ £1.6 billion) to provide immutable records of a gem’s origin, to track it along the supply chain and improve jewellery retailers’ confidence in procurement. [6]
Scalability
As more nodes join a blockchain network, latency and convergence can increase. Compare the transaction speed between Bitcoin, the oldest and biggest public blockchain network which can only process 7 transactions per second, and Visa, a centralised electronic payment network which can handle more than 24,000 transactions per second [7].
Scalability is a challenge in setting up a public blockchain, but there are several options to enhance it:
- Data Sharding – Data sharding splits an extensive blockchain network into smaller, more easily managed parts called shards. A node does not need to rely on the whole database to verify and process a transaction. Instead, all nodes work in parallel, resulting in more efficient transaction throughput.
- Off-chain data storage – Transactions can be completed on the blockchain network, and data is stored in the off-chain environment to reduce the on-chain storage requirements.
- Scalable consensus mechanisms – The Proof of Work consensus protocol in Bitcoin provides a high-security mechanism but a long transaction time. Proof of Stake consensus mechanism is a possible solution to speed up transaction time and higher scalability.
Conclusion
To decide whether to invest in blockchain technology, your team should ascertain whether your business needs will be best met by using this approach and explore cost and revenue impact as much as possible. Equally, you should consider the disadvantages of blockchain technology such as potential cyber-attacks, high energy consumption and scalability concerns to decide how to address each of them. Blockchain technology is not the only way to perform full data transparency or traceability – well-managed centralised databases can solve it.
Blockchain technology changes how we trust and solve problems in a traditional database system, like disintermediation and data security enhancement. It can optimise the operation in low-trust environments where users rely on third-party checks.
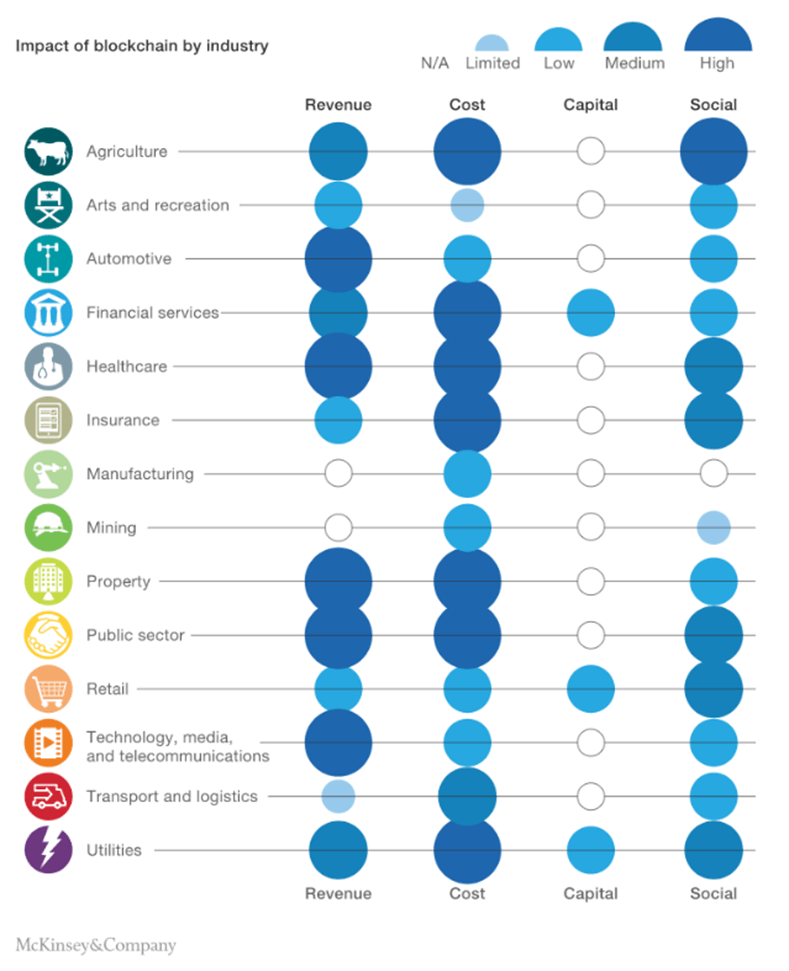
An insight written by McKinsey Digital [8] analysed the monetary impact in more than 90 use cases; they estimated that approximately 70 per cent of the value at stake in the short term is cost reduction, followed by revenue generation and capital relief. Cost can be taken out by removing intermediaries and administrative efforts on housekeeping, as well as improvements in transparency and fraud control.
Specific industries that capture the most significant revenue from blockchain are Automotive, Healthcare, Property, Public Sector and Technology, Media & Telecommunications. We believe the value of blockchain will enable brand-new business models and revenue streams over time.
This is the first blog in our new series which aims to help you understand the different aspects of blockchain technology. Over the course of the series, we will discuss how blockchain impacts data governance, cybersecurity and cyber-attacks.
How CACI can help
Equipping your systems with blockchain-compatible elements is a key initial step. Our services enable you to ensure that the foundations are correct and our experts can advise you on network design, architecture, service design, business process, data governance and cybersecurity solutions. Get in touch with us today.
Notes:
[1] Blockchain Explorer – Search the Blockchain | BTC | ETH | BCH, statistics as of 23 Oct, 2022
[2] Ethereum Chain Full Sync Data Size (ycharts.com), statistics as of 24 Oct 2022
[3] Forbes Blockchain 50 2022
[4] Allianz tops the ranks in Brokerbility’s insurer partner satisfaction survey (insurancetimes.co.uk)
[5] Boeing supports TrustFlight aircraft maintenance project using blockchain – Ledger Insights – blockchain for enterprise
[6] De Beers group introduces world’s first blockchain-backed diamond source platform at scale – De Beers Group
[7] Small Business Retail | Visa
[8] The strategic business value of the blockchain market | McKinsey




 From entering new markets to growing market share, mergers and acquisitions (M&As) can bring big business benefits. However, making the decision to acquire or merge is the easy part of the process. What comes next is likely to bring disruption and difficulty. In research reported by the
From entering new markets to growing market share, mergers and acquisitions (M&As) can bring big business benefits. However, making the decision to acquire or merge is the easy part of the process. What comes next is likely to bring disruption and difficulty. In research reported by the